Just short of a week after its release, the new HTC One has been rooted thanks to Android devs beaups and jcase, the same guys that brought us S-OFF for the original HTC One (M7).
Their exploit, dubbed WeakSauce, gains root, and mounts a new xbin partition containing busybox as well as superuser. While the method was designed for the Verizon variant of the M8, the devs state that it should work for all variants. Although some are reporting that International variants are not playing nice with this method, that's about the worst that can happen—you may not be rooted, but you certainly won't brick your device.

We'll have a full guide for you guys shortly, but until then, check out the instructions below.
How to Root
Making sure you have "Unknown sources" enabled in your Security settings, grab the file for WeakSauce (app mirror), unzip it, and run the app. After it does its thing, head to Google Play and install Chainfire's SuperSU.
Now simply reboot your device and you're rooted! Nice and easy.
What This Method Doesn't Do
Remember, this method re-roots the device on every boot (no permanent root until the M8 gets S-OFF), so give your device about 30 seconds on each boot for the exploit to do its thing.
Because your device doesn't maintain root permanence, using Xposed Framework is somewhat buggy at the moment. The only method of Installing Xposed is to rely on "soft reboots" within the app itself. Meaning, if you install Xposed, update the framework, or activate any modules, make sure to select "soft reboot" from the app's reboot menu.
How to Unroot
As easy as this rooting method is, it's even easier to unroot. Simply uninstall WeakSauce, uninstall SuperSU, and reboot.
How to Update Root
As the method and process are new, we'll probably be seeing quite a few updates from the devs. To update, simple uninstall the two apps just like you would to unroot, then reinstall them after rebooting.
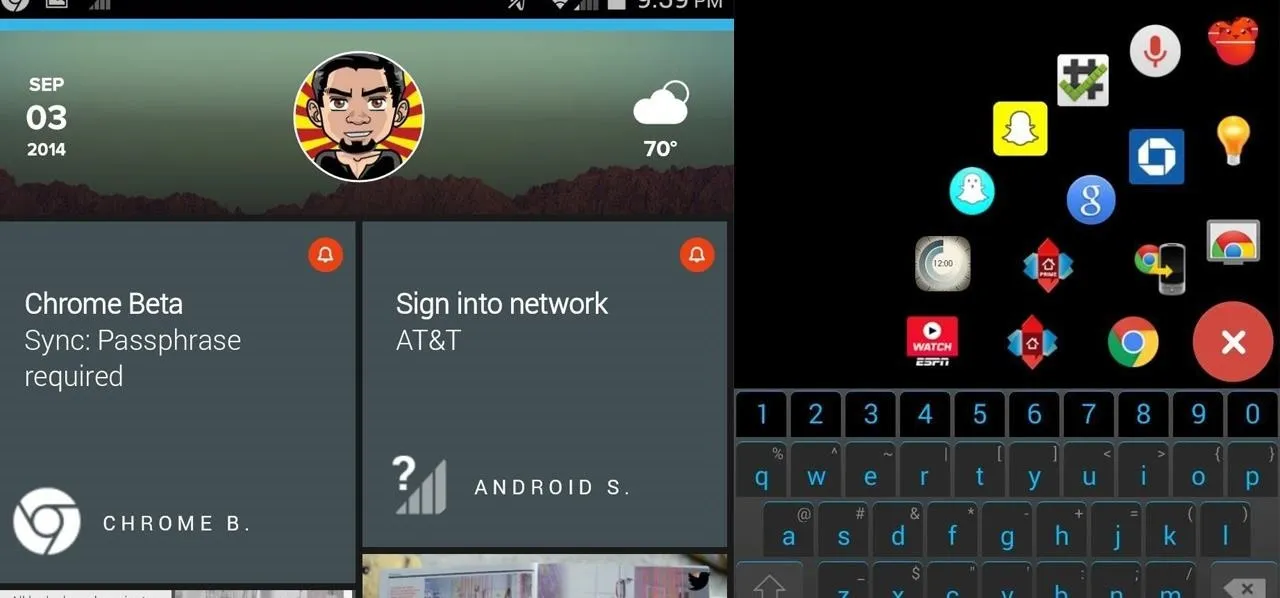
Root checker image via whskytango/XDA


















Comments
Be the first, drop a comment!